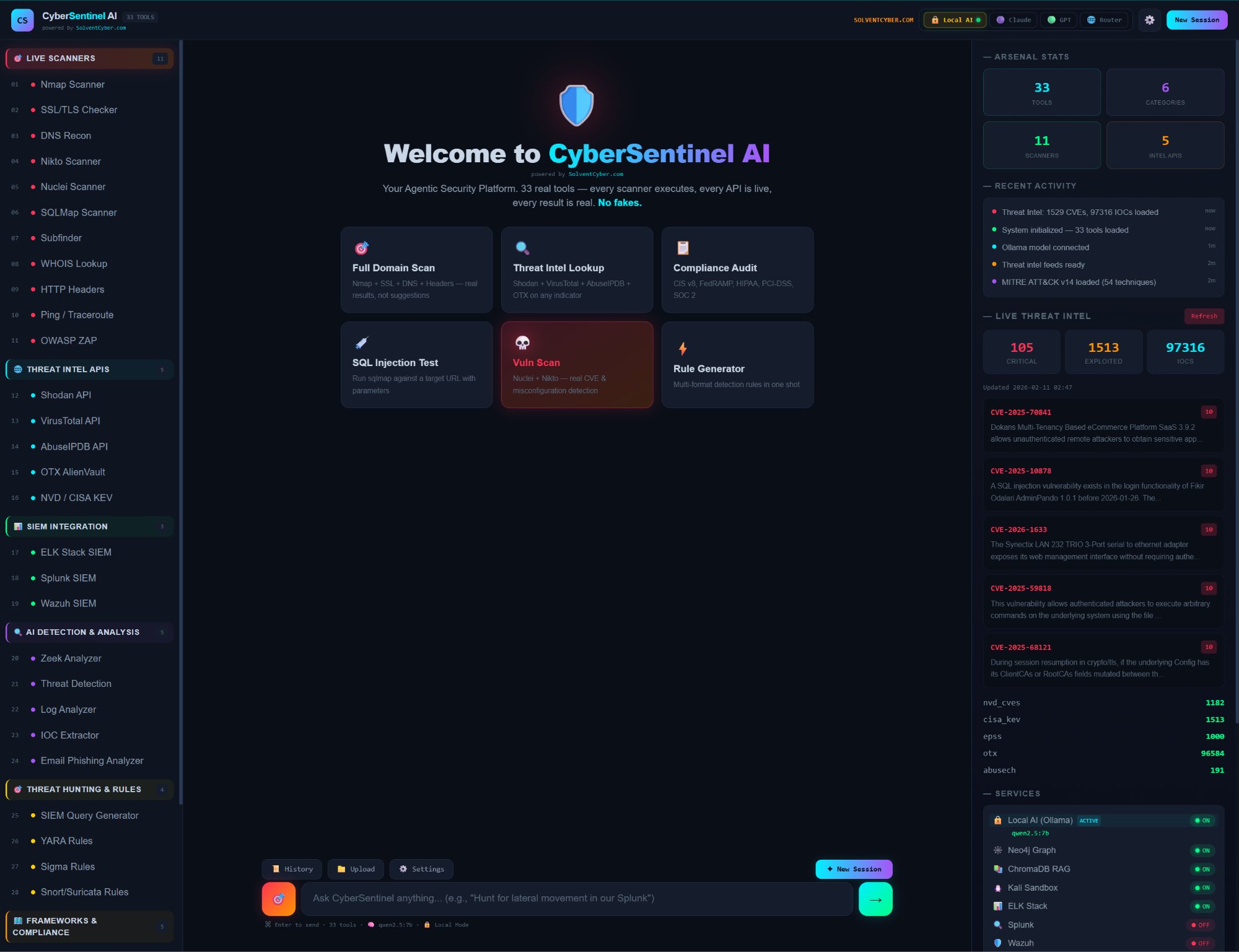
33 Security Tools.
3 AI Brains.
One Platform.
CyberSentinel AI is an agentic cybersecurity platform that runs 33 real security tools locally via Docker — powered by multi-model AI with RAG-grounded knowledge and 4-layer hallucination protection.